Iron Fort User Documentation¶
Training¶
Security Awareness Training¶
HIPAA requires all workforce members who access patient data to complete security training. Iron Fort helps you manage this requirement.
Training Requirements¶
Initial Training: Before anyone gets access to patient data systems
Annual Training: Every year for all workforce members
Role-Specific Training: Additional training based on job responsibilities
Incident-Based Training: When new threats emerge or policies change
Training Program Features¶
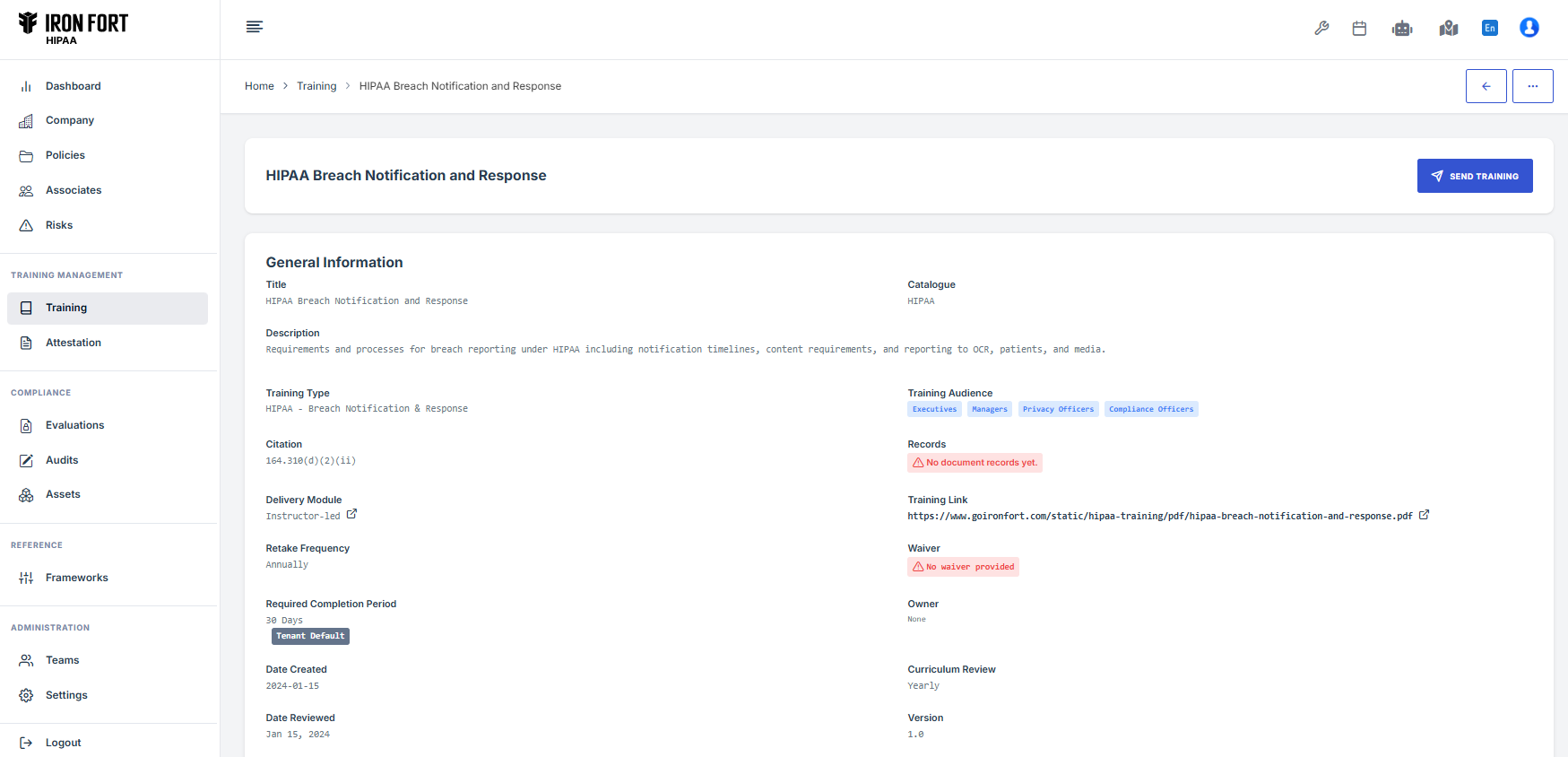
Course Management: - Centralized training library - Automatic assignment based on roles - Progress tracking for all staff - Completion certification - Documentation storage
Required Training Topics:
The platform covers all HIPAA-mandated topics:
-
ePHI Threats and Vulnerabilities
Understanding risks to patient data -
Information Access Control
Who can access what and why -
Password Management
Creating and protecting credentials -
Incident Reporting
How to report security problems -
Malicious Software
Recognizing and avoiding threats -
Social Engineering
Phishing, spear phishing, and vishing -
Log-in Monitoring
Understanding access tracking -
Policies and Procedures
Your organization's rules and requirements
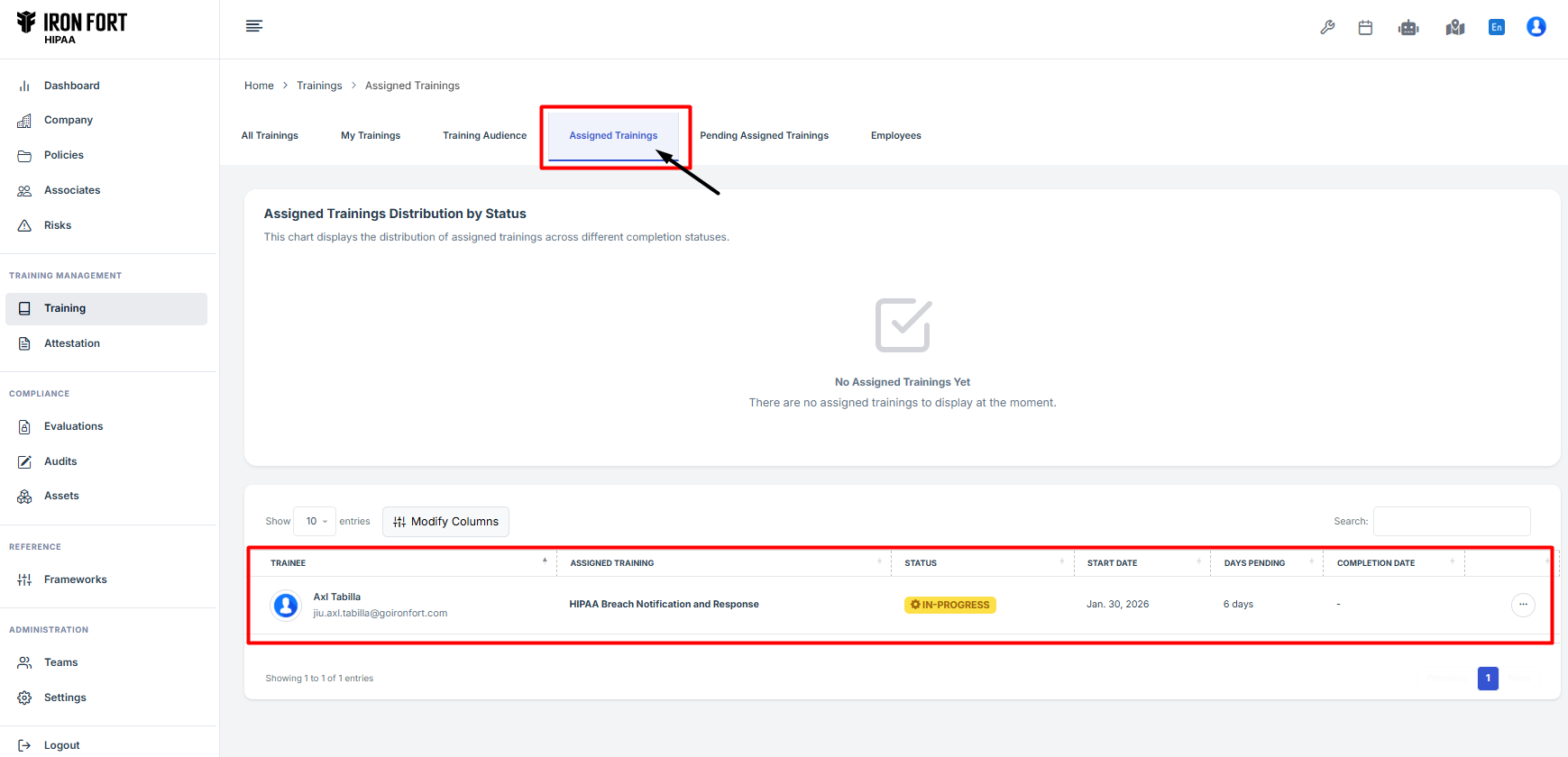
Training Documentation¶
Iron Fort automatically maintains required records: - Participant names - Training dates - Topics covered - Completion status - Certificates issued - Sign-in records
All records are kept for 6 years as required by HIPAA.
Security Reminders¶
Beyond formal training, send periodic security reminders when: - Policies are updated - New security controls are added - Controls are significantly changed - New threats appear - HIPAA rules change - Leadership directs
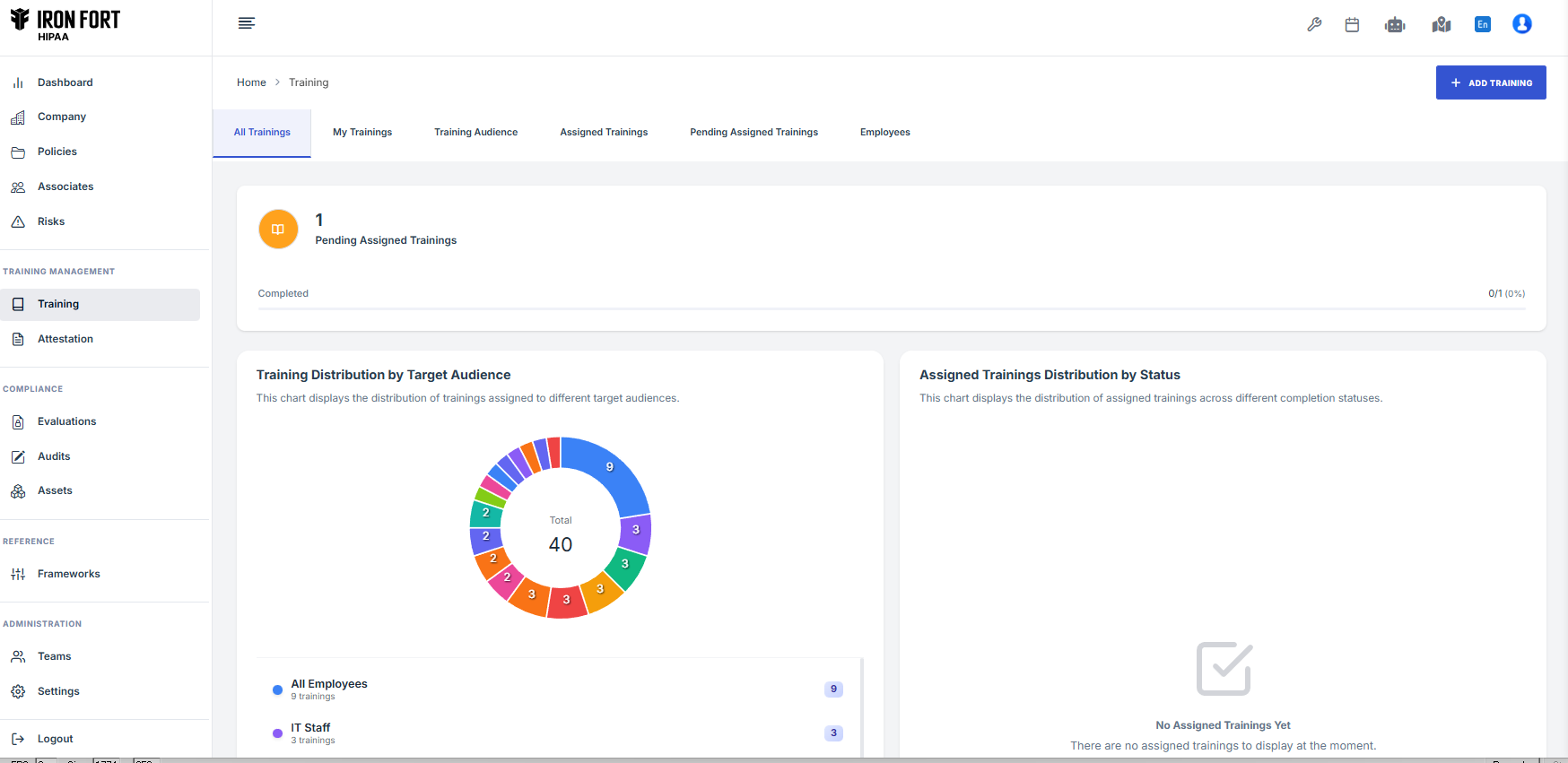
Training Reports¶
Access real-time reports showing: - Completion rates by department - Overdue training assignments - Compliance percentages - Individual training histories - Certification status
Best Practices¶
- Schedule Annual Training: Same time each year for consistency
- New Hire Protocol: Complete before system access granted
- Track Completion: Monitor and follow up on overdue assignments
- Document Everything: Maintain detailed records for audits
- Keep Content Current: Update for latest threats and policies